Attackers in 2026 have a continuous, automated, outside-in view of your organization’s digital exposure. Autonomous scanning systems probe the entire internet constantly, identifying new assets, testing for known weaknesses, and adding findings to target lists with no human operator involved. The time between a new asset appearing on the internet and an attacker discovering it is measured in hours, not weeks.
Against that reality, organizations still conducting annual penetration tests and quarterly vulnerability scans to understand their external risk are not just behind. They are operating with a fundamentally different picture of their exposure than their attackers have. Attack surface management closes that gap.
What Your Attack Surface Actually Includes
Your attack surface is everything that exists on the internet that an external party could potentially find, interact with, or exploit in connection with your organization. For most organizations, this is larger and more complex than their internal asset inventories reflect. Security teams consistently underestimate the size of their external footprint, and it is almost always in the unknown and forgotten assets that the most serious vulnerabilities are found.
| Asset Type | Why It Is a Risk |
|---|---|
| Public-facing websites and web applications | Including older ones never formally retired |
| Cloud infrastructure across multiple providers | Dev environments and storage set up temporarily and never locked down |
| VPNs and remote access portals | Administrative interfaces accessible from the public internet |
| Third-party SaaS and API integrations | Often with broader permissions than necessary |
| Expired or abandoned subdomains | Still resolving and running outdated unpatched software |
| Shadow IT | Tools adopted without IT involvement, outside your security program |
| AI agents and automation tools | New access paths and data exposure nobody has formally inventoried |
Why 2026 Has Made Attack Surface Management More Urgent Than Ever
Several converging factors in 2026 have elevated attack surface management from a security best practice to an operational necessity. Autonomous AI attack tools mean that your external exposure is being evaluated continuously by systems that do not sleep, do not take weekends off, and do not forget to check the subdomains that your team stopped thinking about three years ago.
Cloud adoption has expanded the attack surface significantly for most organizations while simultaneously making it harder to maintain an accurate inventory. Development environments, storage buckets, and API endpoints are created and modified constantly, and the pace of change frequently outstrips the security team’s ability to track it. Shadow AI, where employees adopt AI tools and agents without IT oversight, is a new and rapidly growing category of exactly this problem.
Supply chain risk adds another dimension. When a trusted software vendor or service provider is compromised, the attacker gains access through a trusted relationship that bypasses most of the defenses the target organization has put in place. The most exploited vulnerabilities in 2025 were found in widely deployed enterprise software that organizations had been using for years without treating it as a significant exposure.
The gap between how often organizations formally assess their external exposure and how continuously attackers probe it is the operational window in which most breaches occur. Attack surface management closes that window.
Why Annual Assessments Are No Longer Sufficient
Annual penetration tests and periodic vulnerability assessments made reasonable sense when digital environments changed slowly and attacker timelines were measured in weeks. Neither of those conditions applies in 2026. New assets are being added to your external footprint continuously. Cloud configurations change daily. A vulnerability that did not exist in your environment on Monday can be present, discovered by an automated scanner, and actively targeted by Wednesday.
A security posture that is accurate in January is not the same security posture in March. Organizations that cannot demonstrate continuous visibility into their external exposure are increasingly finding that position difficult to defend, both to regulators and to their own leadership.
What a Mature Attack Surface Management Program Looks Like
Effective attack surface management runs as a continuous cycle. Here is what each stage delivers:
01. Discovery
Automatically identifies all internet-facing assets associated with your organization, including the ones that nobody on the security team is actively thinking about.
02. Inventory and classification
Builds a live, always-current picture of what exists, who owns it, and how critical it is to the business.
03. Risk prioritization
Surfaces the highest-priority exposures first, based on exploitability, business impact, and current attacker interest. Lets your team direct limited time to what matters most.
04. Remediation tracking
Ensures that fixes are validated rather than just marked as complete.
05. Continuous monitoring
Closes the loop, ensuring that new exposures are identified as they emerge rather than waiting for the next scheduled assessment window.
The Compliance Dimension
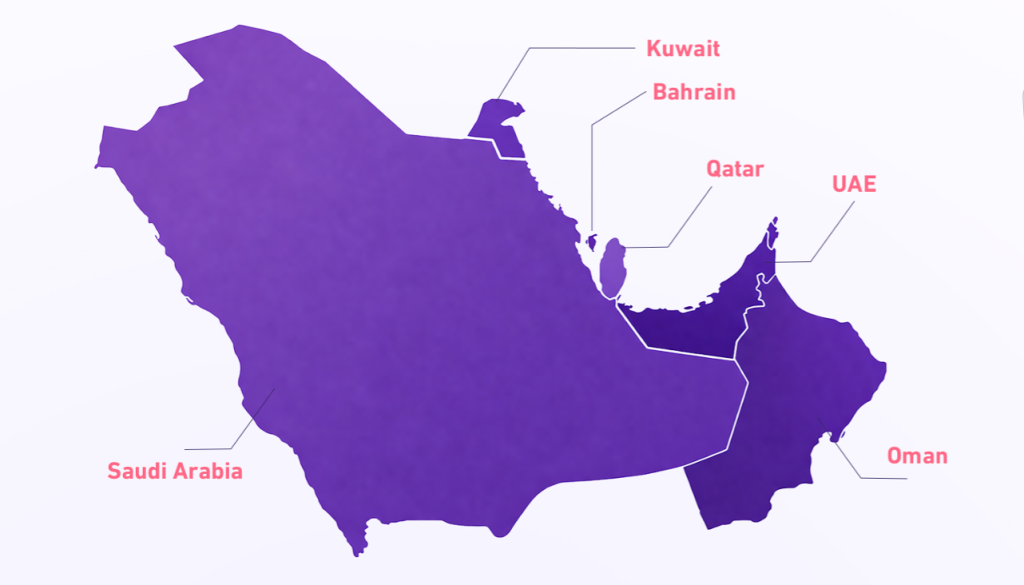
From a regulatory standpoint, continuous attack surface management supports requirements across multiple frameworks that Saudi and GCC organizations operate under, including the NCA Essential Cybersecurity Controls and SAMA’s updated 2026 financial sector requirements. Regulators increasingly expect to see evidence of ongoing monitoring rather than point-in-time audit artifacts. An attack surface management program that generates continuous, time-stamped records of your external exposure and your response to findings is exactly the kind of evidence that a mature compliance posture requires.
How CyberCube Delivers Attack Surface Management
CyberCube’s attack surface management solution provides continuous, outside-in visibility into your entire external digital footprint. We automatically discover and monitor your assets, surface exposures with contextual risk scoring, and present findings through an intuitive dashboard that gives your security team clarity on what to address and in what order.
Frequently Asked Questions
What is attack surface management?
Attack surface management is the continuous process of discovering, inventorying, classifying, and monitoring all internet-facing assets associated with an organization. It provides ongoing visibility into external exposure so that security teams can identify and remediate risks before attackers exploit them.
Why is attack surface management important in 2026?
In 2026, autonomous AI scanning tools probe the entire internet continuously. The time between a new asset appearing online and an attacker discovering it is measured in hours. Annual or quarterly assessments cannot keep pace with this threat reality. Continuous attack surface management is now an operational necessity.
What is included in an organization’s attack surface?
An organization’s attack surface includes all public-facing websites and applications, cloud infrastructure, VPNs and remote access portals, third-party SaaS integrations, abandoned subdomains, shadow IT, and AI tools adopted without IT oversight. Most organizations have a significantly larger external footprint than their internal inventories reflect.
How is attack surface management different from penetration testing?
Penetration testing is a point-in-time exercise conducted periodically. Attack surface management is continuous. It provides ongoing monitoring of your external exposure rather than a snapshot that may be outdated within days of completion.
Does attack surface management help with regulatory compliance in Saudi Arabia and the GCC?
Yes. Continuous attack surface management supports compliance with the NCA Essential Cybersecurity Controls and SAMA’s 2026 financial sector requirements. It generates time-stamped records of external exposure and remediation activity that regulators increasingly require as evidence of ongoing monitoring.
How does CyberCube’s attack surface management work?
CyberCube provides continuous, outside-in visibility across your entire external digital footprint. Our solution automatically discovers and monitors assets, surfaces exposures with contextual risk scoring, and delivers findings through a clear dashboard so your team always knows what to prioritize.
See your attack surface the way attackers do
Explore CyberCube Attack Surface Management