Introduction
The relationship between geopolitics and cybersecurity has never been more direct. As GCC cyber threats continue to rise in line with regional tensions, organizations across the Gulf are finding themselves in the crossfire. When regional tensions escalate, threat actors mobilise. Networks are probed, systems are targeted, and organizations are left exposed before they even realise it. Over a 39-day observation window spanning February 28 to April 8, 2026, CyberCube’s threat intelligence team tracked adversary activity across the Middle East. Every GCC state recorded exposure. No sector was untouched. Here is what we found.By The Numbers
|
1,798 Total adversary claims recorded across the Middle East |
935 DDoS claims recorded against critical services |
26 Ransomware claims targeting Gulf organizations |
60% Of all claims targeted public sector entities |
How Adversaries Operated
Understanding how adversaries operate is as important as knowing the volume of claims recorded.| Claim Type | Share |
|---|---|
| DDoS | 52% |
| Defacement | 30% |
| Data Breach | 10% |
| Data Leak | 5% |
| Other | 3% |
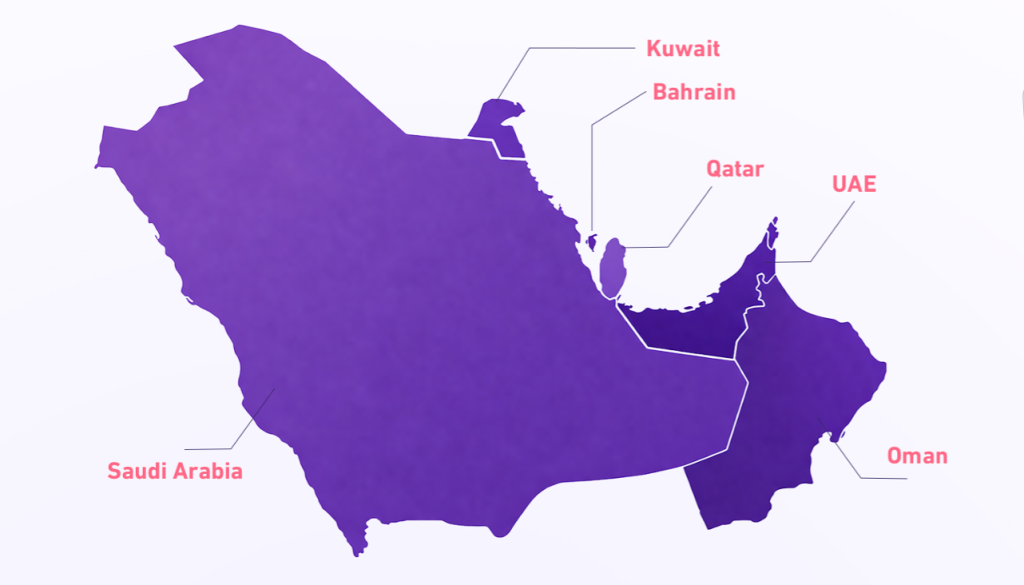
GCC Cyber Threat Exposure by Country
The data shows that no Gulf state was spared. Claim volumes varied across the region, reflecting differences in digital footprint, strategic significance, and sector exposure.| Country | Total Claims |
|---|---|
| UAE | 242 |
| Kuwait | 145 |
| Saudi Arabia | 100 |
| Bahrain | 94 |
| Qatar | 69 |
| Oman | 11 |
Who Was Targeted
| Industry | Share of Claims |
|---|---|
| Public Sector | 60.1% |
| Education | 11.5% |
| Telecommunications | 10.1% |
| Financial Services | 9.7% |
| Transportation | 8.6% |
The Threat Actors Behind It
Five groups were identified as most active during this observation window:| # | Threat Actor |
|---|---|
| 01 | Keymous+ |
| 02 | DieNet |
| 03 | 313 Team |
| 04 | L4663R666H05T |
| 05 | Handala |
Important: These actors remain active. The end of a geopolitical event does not mark the end of the threat.
What This Means For Your Organization
01. Geopolitical events are now cyber events Regional tensions directly translate into elevated cyber risk. Monitoring the geopolitical environment is now a core part of effective threat intelligence.
02. Public sector cannot afford complacency With 60% of claims hitting public sector entities, state-linked organizations must treat cyber resilience as a board-level priority.
03. Threat actor access outlasts the headlines Actors who establish access during peak tension periods retain that access long after the geopolitical moment passes. De-escalation is not the all-clear.
04. Situational awareness is non-negotiable Organizations without visibility into their threat landscape are operating blind. Knowing who is targeting you, and how, is the foundation of effective defence.
Frequently Asked Questions
What is a GCC cyber threat?
A GCC cyber threat refers to any adversarial cyber activity targeting organizations across the Gulf Cooperation Council states, including Saudi Arabia, UAE, Kuwait, Bahrain, Qatar, and Oman. These threats include DDoS claims, data breaches, defacement, and ransomware campaigns.How many cyber claims were recorded in the GCC during the regional escalation?
CyberCube’s threat intelligence team recorded 1,798 total adversary claims across the Middle East over a 39-day window from February 28 to April 8, 2026. Every GCC state recorded exposure during this period.Which GCC country recorded the most cyber claims?
The UAE recorded the highest volume of claims among GCC states with 242 claims, followed by Kuwait with 145 and Saudi Arabia with 100.Which industries were most targeted by cyber threat actors in the GCC?
Public sector organizations were the most heavily targeted, accounting for 60.1% of all claims. Education, telecommunications, financial services, and transportation followed as the most affected sectors.What types of cyber claims were most common during this period?
DDoS claims were the most common at 52%, followed by defacement at 30%, data breach at 10%, data leak at 5%, and other claim types at 3%.Who were the top threat actors active in the GCC during this period?
The five most active threat actor groups identified were Keymous+, DieNet, 313 Team, L4663R666H05T, and Handala. These groups remain active beyond the observation window.How can organizations in the GCC protect themselves from cyber threats?
Organizations should invest in continuous threat intelligence, proactive attack surface monitoring, and robust incident response capabilities. Staying aware of both the geopolitical environment and the cyber threat landscape is essential for effective defence.Conclusion
This 39-day window is a snapshot of a broader reality. Cyber threats do not operate in isolation. They are shaped by the world around them. As geopolitical dynamics across the Middle East continue to evolve, so will the GCC cyber threat landscape facing Gulf organizations. Those who invest in continuous threat intelligence and proactive monitoring will be best positioned for what comes next.Stay aware of your threat landscape