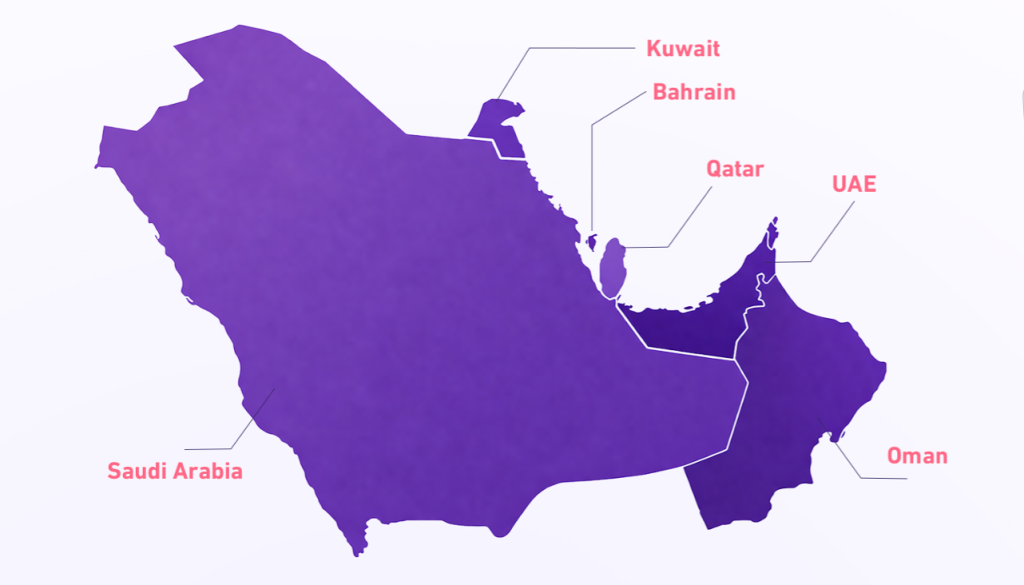
Saudi Arabia is facing a surge in cybersecurity threats in 2026, and the environment has not quieted down. The threat landscape has shifted meaningfully over the past twelve months, and the organizations seeing the worst outcomes are those still operating on assumptions that were formed two or three years ago. This article covers what is actually happening in 2026 and what Saudi organizations need to be paying attention to right now.
Autonomous AI Attacks Have Changed the Pace of Everything
The most significant shift in 2026 is the use of autonomous, or agentic, AI systems on the attacker side. Unlike earlier AI tools that assisted human operators, these systems can set objectives, execute multi-step attack sequences, adapt when blocked, and continue operating without any human involvement after the initial instruction is given. The practical result is that attacks which previously required days of skilled human effort can now be delegated to an automated system that runs around the clock.
For Saudi organizations, this means the window between a vulnerability being discovered and an attack being launched has compressed dramatically. Attackers are scanning, probing, and escalating access at a pace that manual security processes simply cannot match. The organizations that were already investing in continuous monitoring have a meaningful advantage over those still relying on scheduled assessments.
The threat is no longer a skilled human sitting at a keyboard. It is an automated system with a goal and the persistence to keep trying until it achieves it or gets shut down.
Identity Is the Primary Battleground
Across Saudi Arabia and the wider GCC, the most common entry point for attacks in 2026 is not a technical exploit. It is a stolen credential. Attackers are logging in with legitimate usernames and passwords rather than breaking through technical defenses. This approach is faster, cheaper, and significantly harder to detect than traditional intrusion methods.
The credential economy on underground marketplaces has grown substantially. Verified access to Saudi corporate networks, banking platforms, and public sector systems is actively traded. Once an attacker has a working credential, they often sit quietly for extended periods, mapping the environment and waiting for the right moment to act, before any visible damage occurs.
The 2026 updates to both the NCA’s frameworks and SAMA’s financial sector requirements directly address this, now requiring organizations to implement continuous, context-aware identity verification rather than relying on static passwords and periodic authentication checks.
Ransomware Groups Operate Like Businesses Now
The ransomware ecosystem has matured into something that more closely resembles a commercial industry than a criminal subculture. Groups operate with specialized roles, defined processes, customer service for victims negotiating payments, and affiliate networks that extend their reach without requiring them to conduct every attack directly. Access to a compromised Saudi corporate network can be packaged, priced, and sold to a ransomware operator in under a minute.
Healthcare, financial services, logistics, and public infrastructure have all seen significant ransomware activity in the Kingdom. The attacks are not opportunistic. Targets are researched, access is purchased from brokers, and the timing and scale of encryption events are planned to maximize pressure on victims. Double extortion, where data is both encrypted and threatened for public release, is now the standard playbook rather than the exception.
| Sector | Why It Is Targeted |
|---|---|
| Healthcare | Patient data commands premium prices and downtime is operationally catastrophic |
| Financial services | Face both ransomware and precision credential attacks on high-value accounts |
| Logistics and supply chain | Disruption affects multiple downstream clients simultaneously |
| Technology vendors | Hold access to multiple client environments making them high-value targets |
The Dark Web Market for Saudi Data Is Active and Specific
Dark web forums in 2026 contain a substantial and growing volume of material specifically targeting Saudi and GCC organizations. This is not incidental. The Gulf region’s high transaction values, rapid digital adoption, and growing attack surface make it commercially attractive to criminal operators. Listings for verified access to Saudi corporate infrastructure, stolen customer databases from financial institutions, and packaged credential sets tied to specific Saudi domains are regularly observed by threat intelligence teams monitoring these spaces.
Hacktivist activity has also increased alongside financially motivated attacks. DDoS campaigns targeting Saudi organizations have risen sharply, with public sector agencies, banking institutions, and national infrastructure being the most common targets. These campaigns are often tied to regional geopolitical events and can appear with little warning.
Supply Chain Attacks Are a Growing Blind Spot
Saudi organizations typically have strong visibility into their own systems and considerably less visibility into the security posture of the vendors, software providers, and managed service partners they depend on. Attackers have recognized and are actively exploiting this gap. By compromising a trusted third party, a single intrusion can cascade into access across dozens of client organizations simultaneously.
Cloud service adoption across the Kingdom has accelerated this risk. Every SaaS platform, API integration, and outsourced technology function represents a potential entry point that sits partially or entirely outside the organization’s direct security controls. The attack does not need to come through your front door if there is an unmonitored side entrance through a supplier’s compromised system.
Post-Quantum Harvesting: The Threat With a Long Fuse
A less visible but genuinely serious threat in 2026 is the systematic collection of encrypted data by attackers who intend to decrypt it later, once quantum computing capability matures. Sensitive data that is strongly encrypted today may not remain secure within the next few years if current projections about quantum computing development prove accurate.
Who should treat this as an active risk now:
Organizations that handle long-lived sensitive data including financial records, healthcare information, legal documents, and strategic planning materials should be treating post-quantum harvesting as an active risk management issue rather than a distant theoretical concern.
How CyberCube Addresses These Threats
CyberCube’s platform is built for the speed and complexity of the 2026 threat environment. Our continuous monitoring across brand presence, external attack surface, and dark web activity means that threats are identified as they emerge rather than after they have caused damage. Our AI-driven intelligence converts the volume and complexity of today’s threat landscape into specific, actionable signals that your team can act on quickly.
Frequently Asked Questions
What are the biggest cybersecurity threats facing Saudi Arabia in 2026?
The biggest cybersecurity threats in Saudi Arabia in 2026 include autonomous AI-powered attacks, credential theft and identity-based intrusions, ransomware targeting healthcare and financial services, dark web trading of Saudi corporate data, supply chain vulnerabilities, and post-quantum data harvesting.
How have AI-powered attacks changed cybersecurity in Saudi Arabia?
Autonomous AI attack systems can now execute multi-step attack sequences, adapt when blocked, and operate continuously without human involvement. This has compressed the window between vulnerability discovery and active exploitation to hours, making continuous monitoring essential for Saudi organizations.
Why are Saudi organizations targeted on the dark web?
The Gulf region’s high transaction values, rapid digital adoption, and growing digital footprint make Saudi organizations commercially attractive to criminal operators. Verified access credentials, stolen customer databases, and packaged credential sets tied to Saudi domains are actively traded on underground marketplaces.
What is double extortion ransomware?
Double extortion is a ransomware tactic where attackers both encrypt an organization’s data and threaten to publicly release it unless a ransom is paid. This creates dual pressure on victims and has become the standard approach used by ransomware groups targeting Saudi organizations in 2026.
What is post-quantum harvesting and why does it matter for Saudi organizations?
Post-quantum harvesting is the practice of collecting strongly encrypted data today with the intention of decrypting it once quantum computing matures. Organizations in Saudi Arabia that handle long-lived sensitive data such as financial records, healthcare information, and legal documents should treat this as an active risk management priority.
How does supply chain risk affect Saudi cybersecurity?
Saudi organizations often have strong visibility into their own systems but limited visibility into their vendors and managed service partners. Attackers exploit this by compromising trusted third parties to gain indirect access to Saudi corporate environments. Every SaaS platform and API integration represents a potential entry point outside the organization’s direct control.
What do the NCA and SAMA require from Saudi organizations in 2026?
The 2026 updates to both the NCA Essential Cybersecurity Controls and SAMA’s financial sector requirements now require Saudi organizations to implement continuous, context-aware identity verification rather than relying on static passwords and periodic authentication checks.
Stay ahead of the 2026 threat landscape
Explore CyberCube’s threat intelligence platform