Brand impersonation has always been a problem for large, recognizable companies. In 2026, it has become an industrialized operation. Across the GCC, attackers are running coordinated campaigns that clone websites, generate AI-crafted customer interactions, and operate fake brand presences across multiple digital channels simultaneously. The scale, speed, and technical sophistication of what is happening now is meaningfully different from what organizations were dealing with even two years ago.
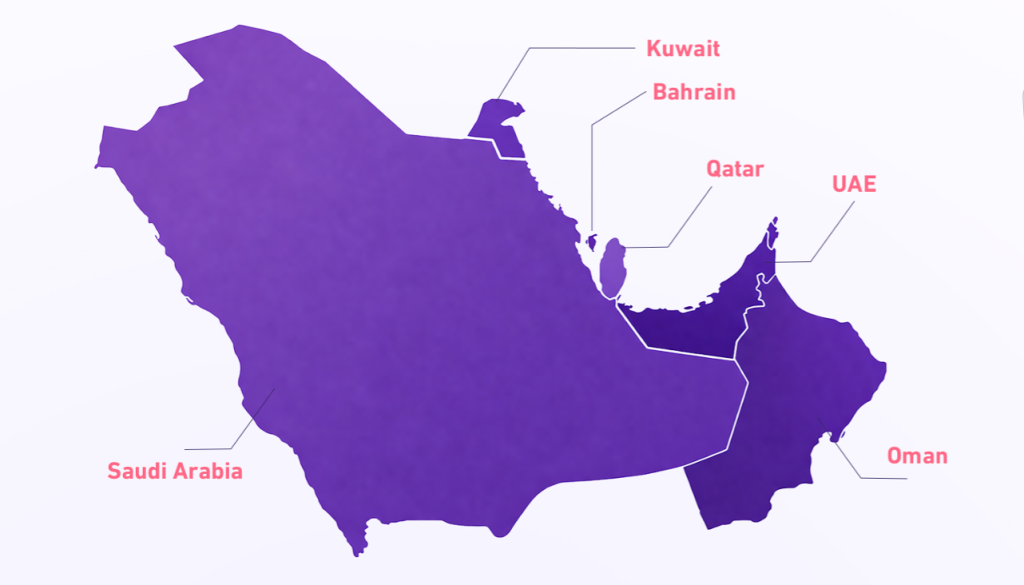
The Gulf is a particularly attractive target. High average transaction values, rapid digital adoption, a growing base of new digital users, and the visibility that comes with being one of the world’s most economically significant regions all make it commercially appealing to criminal operators. Both Saudi Arabia and the UAE consistently appear among the most targeted nations in the region, and the attack volume is not decreasing. Effective brand protection in the GCC has never been more critical.
What Has Actually Changed in 2026: AI-Powered Brand Impersonation at Scale
The defining shift in brand impersonation in 2026 is the use of AI to automate what was previously labor-intensive work. Website cloning that once took hours now takes minutes. Convincing phishing content in perfect, native-level Arabic is generated at scale from stolen customer data. Customer service agents that respond to victim queries in real time, maintaining the illusion of legitimacy through entire conversations, can now be deployed without a human operator involved.
Deepfake technology has advanced to a point where AI-generated audio and video impersonating executives, customer service representatives, or brand spokespeople can no longer be reliably identified as fake by the average viewer or listener. The voice of someone your customers trust is no longer a reliable signal that they are actually communicating with that person.
A fake brand presence that would have required a skilled team of social engineers to operate in 2022 can now be run almost entirely by automated systems in 2026. The economics of brand impersonation have changed completely.
How a Modern Brand Impersonation Attack Is Structured
The process has become faster and more automated, but the structure is consistent. A threat actor identifies a high-value Gulf brand, typically in banking, telecom, logistics, retail, or public utilities. A lookalike domain is registered, often using a minor spelling variation, an added word, or a regional domain suffix. The legitimate website is cloned automatically. Customers are then driven to the fake site through a combination of targeted SMS campaigns, WhatsApp messages, and sometimes paid search advertising that places the fraudulent site above legitimate results for your own brand name.
| Attack Method | How It Works |
|---|---|
| Lookalike domains | Typos, regional suffixes, or added words that customers miss at a glance |
| AI-powered chat agents | Handle real customer queries to maintain the illusion of legitimacy |
| Deepfake audio and video | Executives making fake investment or promotional claims |
| SMS and WhatsApp campaigns | Reference real account details sourced from earlier breaches |
| Fraudulent paid search ads | Appearing above legitimate brand results for your own brand name |
| Fake social media accounts | Built quickly with AI-generated content and engagement |
DDoS Is Being Used Alongside Impersonation, Not Separately
A pattern that has become more common in the GCC in 2026 involves using a DDoS attack to take a legitimate website offline, then driving confused traffic to a fake site that has been prepared in advance. Customers unable to reach the real site and unaware that an attack is in progress visit the fraudulent version instead. The two tactics together are considerably more effective than either one in isolation. DDoS attacks targeting Gulf organizations have increased substantially, with public sector entities, banks, and national infrastructure among the most frequently targeted.
The Full Scope of Brand Abuse in 2026
Most organizations think of brand impersonation as fake websites. The reality in 2026 is considerably broader.
Social media impersonation
Fake accounts using your logo and brand identity to run fraudulent promotions or scam campaigns are widespread across Instagram, X, LinkedIn, and Snapchat.
Mobile app cloning
Fraudulent apps published on unofficial stores mimic your legitimate application and are a growing channel for credential and payment theft.
Fraudulent WhatsApp customer service accounts
Particularly active in Arabic-speaking markets, directing customers to provide credentials or payment details to fake agents.
The Cost Goes Well Beyond the Immediate Fraud
The direct costs of a brand impersonation campaign — fraud losses, chargebacks, and incident response — are real. The longer-term costs are harder to quantify but often more significant. Customer trust, once eroded by an impersonation incident, does not automatically return when the fake site is taken down. Customers who were defrauded, or who heard about others being defrauded through what appeared to be your brand, make different decisions about whether to continue using your services.
Regulatory exposure is also growing. As GCC regulators including the NCA and the UAE Cybersecurity Council increase their focus on customer protection standards, failure to actively monitor for and respond to brand impersonation is increasingly treated as a compliance issue rather than purely an operational one.
What Effective Brand Protection in the GCC Looks Like Now
Effective brand protection means detecting threats before your customers encounter them. That requires continuous, automated monitoring across new domain registrations, social media platforms, app stores, and dark web channels where your brand data may be traded or your targeting discussed. When something is found, rapid takedown capability matters enormously. A fake site that is active for 24 hours creates far more harm than one identified and removed within a couple of hours of appearing.
How CyberCube Protects Gulf Brands
CyberCube’s brand protection GCC solution was built for the Gulf market. We monitor continuously across Arabic-language platforms and regional domain registrars that tools built for other markets miss. When a threat is identified, we provide the intelligence and the takedown support so your team is not navigating an unfamiliar and time-sensitive process without help.
Frequently Asked Questions
What is brand protection in cybersecurity?
Brand protection in cybersecurity refers to the continuous monitoring and takedown of fraudulent digital assets that impersonate an organization. This includes fake websites, lookalike domains, fraudulent social media accounts, cloned mobile apps, and deepfake content using executive identities.
How common is brand impersonation in the GCC?
Brand impersonation is one of the fastest-growing cyber threats in the GCC. Both Saudi Arabia and the UAE consistently appear among the most targeted nations in the region. In 2026, AI-powered tools have made it possible to run coordinated impersonation campaigns at a scale and speed that was not previously possible.
What industries are most targeted by brand impersonation in the Gulf?
Banking, telecommunications, logistics, retail, and public utilities are among the most frequently targeted industries in the GCC. These sectors have high customer transaction volumes and strong brand recognition, making them commercially attractive to criminal operators.
How does AI change brand impersonation attacks?
AI has automated previously labor-intensive attack methods. Website cloning that once took hours now takes minutes. Convincing phishing content in native-level Arabic is generated at scale. AI-powered chat agents can maintain fraudulent customer interactions in real time. Deepfake audio and video of executives can no longer be reliably identified as fake.
What is the difference between a lookalike domain and a legitimate website?
A lookalike domain is a fraudulent web address designed to closely resemble a legitimate brand’s domain. Attackers use minor spelling variations, added words, or regional domain suffixes to register domains that customers miss at a glance. These domains host cloned versions of legitimate websites used to steal credentials and payment information.
How does CyberCube’s brand protection work in the GCC?
CyberCube monitors continuously across Arabic-language platforms, regional domain registrars, social media channels, app stores, and dark web sources that tools built for Western markets consistently miss. When a threat is identified, CyberCube provides both the intelligence and takedown support to remove it rapidly.
Is brand impersonation a compliance issue for GCC organizations?
Yes. GCC regulators including the NCA and the UAE Cybersecurity Council are increasingly treating failure to monitor and respond to brand impersonation as a compliance matter. Organizations are expected to demonstrate active brand protection measures rather than respond reactively after customer harm has occurred.
Protect your brand before your customers are harmed