Most organizations find out they have been breached from someone else. A law enforcement notice. A security researcher’s disclosure. A partner who spotted something. Or the attacker themselves, via a ransom note. By the time any of those notifications arrive, the stolen data has typically been on the dark web for weeks, sometimes months, being sold, combined with other stolen datasets, and actively used.
This is not a theoretical risk. The dark web data economy in 2026 is more organized, more commercially sophisticated, and more specifically targeted at regional organizations than it has ever been. Understanding how dark web monitoring works and how to get visibility into it is now a fundamental part of operating a secure organization.
What the Dark Web Actually Is and Why It Matters to Your Business
The dark web is the portion of the internet that standard search engines do not index and that requires specific software to access. Within it sit underground marketplaces, private forums, ransomware leak sites, and communication channels where stolen data, verified access credentials, and cybercrime tools are bought and sold as commodities.
What has changed significantly in 2026 is the integration of AI into how that data is processed and exploited. Attackers are using automated systems to analyze stolen credential sets at scale, to cross-reference data from multiple breaches to build richer target profiles, and to generate convincing phishing and social engineering content in multiple languages from the data they have harvested. The time between a credential appearing on the dark web and it being used in an active attack has shortened considerably as a result.
What Is Being Sold and Who Is Buying It
The range of data available on dark web markets in 2026 is broad. Employee login credentials, increasingly packaged with the associated session tokens that allow attackers to bypass multi-factor authentication entirely, are among the most actively traded items. Customer databases containing personal identification data, financial records, and contact information are consistently available. Verified initial access listings, where a broker has tested and confirmed access to a specific corporate network and is selling that access to the highest bidder, have become a major category of dark web commerce.
| What Is Being Sold | Why It Is Dangerous |
|---|---|
| Login credentials and session tokens | Bypasses MFA entirely |
| Customer databases | Enables targeted fraud and phishing |
| Verified initial access to corporate networks | Sold to ransomware groups directly |
| Healthcare records | Premium pricing for identity fraud |
| API keys and OAuth tokens | Direct access to cloud infrastructure |
| Internal documents and contracts | Competitive and reputational damage |
Why the Probability That Your Data Is Already Out There Is Higher Than You Think
The volume of cyber incidents globally has grown substantially year over year, and the vast majority of breaches involve data that was previously protected by credentials that have since been compromised elsewhere. If your employees reuse passwords across personal and professional accounts, if any of your suppliers or software vendors has been breached, or if your organization has been targeted in any previous attack that was not fully investigated, there is a meaningful probability that some form of data associated with your organization is circulating in underground markets.
The more important question is not whether your data is out there, but whether you know about it, in what form it exists, how current it is, and what exposure it creates. That requires monitoring, not hoping for the best.
The gap between when your data appears on the dark web and when your organization becomes aware of it is where the most damage happens. Closing that gap is what dark web monitoring is for.
5 Warning Signs Your Organization Should Take Seriously
01. Employees locked out of accounts unexpectedly
Login activity appearing from unexpected locations or devices is often the earliest detectable sign that credentials are already in active use by someone else.
02. Suspiciously accurate phishing campaigns targeting your customers
When phishing attempts include specific personal details about your customers, it is a strong indicator that customer data from your systems has already been compromised.
03. Unusual activity in cloud environments or business applications
After-hours access, bulk data exports, or unexpected permission changes frequently follow credential compromise where an attacker is mapping the environment before acting.
04. Spike in fraudulent transactions or account takeovers
An unexplained increase in fraudulent activity is often the first operationally visible sign that a stolen credential set is being actively exploited.
05. Notification from a third party
If you are hearing about your own breach from a partner, regulator, researcher, or law enforcement, your detection capability needs serious attention.
Why You Cannot Do This Manually
The scale and nature of dark web monitoring makes manual approaches unworkable. There are thousands of forums, marketplaces, and communication channels operating simultaneously. Many require established trust within criminal communities to access. Content appears in multiple languages. The platforms themselves shift constantly, migrating to avoid law enforcement attention. And attempting to access these environments without proper infrastructure creates real risks, including malware exposure and potential legal complications.
Effective dark web monitoring requires automated, continuous surveillance combined with human analysis, running across the full breadth of underground activity rather than just the accessible surface layer.
How CyberCube’s Dark Web Monitoring Works
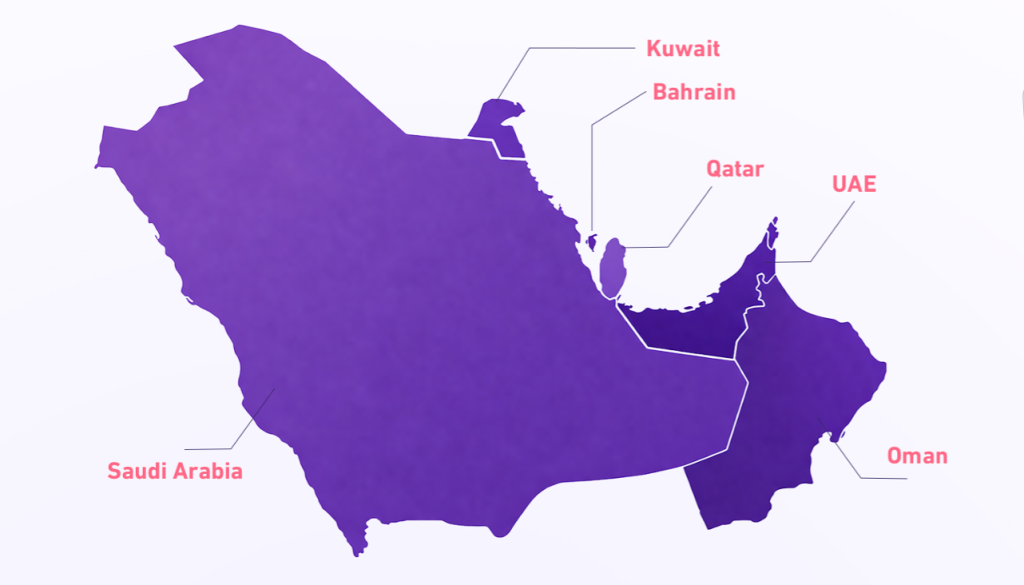
CyberCube provides real-time dark web monitoring built for organizations operating in the Middle East and beyond. Our coverage spans Arabic-language forums and regional marketplaces that tools built primarily for Western markets consistently miss, alongside the global underground ecosystem where data about your organization may surface.
We deliver prioritized, actionable alerts with full context: what was found, where, how recent it is, and what your team needs to do about it. No data dumps. No noise. No false reassurance from a clean report that only searched the easy places.
Frequently Asked Questions
What is dark web monitoring?
Dark web monitoring is the continuous surveillance of underground forums, marketplaces, ransomware leak sites, and private channels to detect when an organization’s data, credentials, or information appears. It provides early warning before stolen data is actively exploited.
How do I know if my organization’s data is on the dark web?
The most reliable way is through dedicated dark web monitoring. Warning signs include unexpected account lockouts, unusual login activity, targeted phishing against your customers, and third-party breach notifications. CyberCube’s dark web monitoring service provides continuous visibility across Arabic and global underground markets.
What data is most commonly found on the dark web?
The most commonly traded data includes employee login credentials, session tokens, customer databases, verified initial access to corporate networks, healthcare records, API keys, and internal business documents.
How quickly can stolen data be used after appearing on the dark web?
In 2026, the time between a credential appearing on the dark web and being used in an active exploit has shortened significantly due to AI-powered automation. Threat actors can process and deploy stolen credentials within hours of acquisition.
Why do Middle East organizations need specialized dark web monitoring?
Many global dark web monitoring tools are built primarily for Western markets and miss Arabic-language forums and regional underground marketplaces where data about Middle East organizations is actively traded. Specialized coverage of these regional channels is essential for accurate threat visibility.
Can my IT team monitor the dark web themselves?
Manual dark web monitoring is not practical at scale. Thousands of forums and channels operate simultaneously, many requiring established criminal community access. Automated, continuous monitoring combined with expert human analysis is the only effective approach.
Find out if your data is already out there
Explore CyberCube Dark Web Monitoring